Google Uncovers DarkSword iOS Zero-Day Spyware CampaignGoogle Uncovers DarkSword iOS Zero-Day Spyware Campaign

- Google linked DarkSword to six zero-days used to breach iPhones in four nations
- DarkSword breached iPhones with six flaws and deployed three spyware strains fast
- Researchers tied DarkSword to vendors and espionage groups in several campaigns
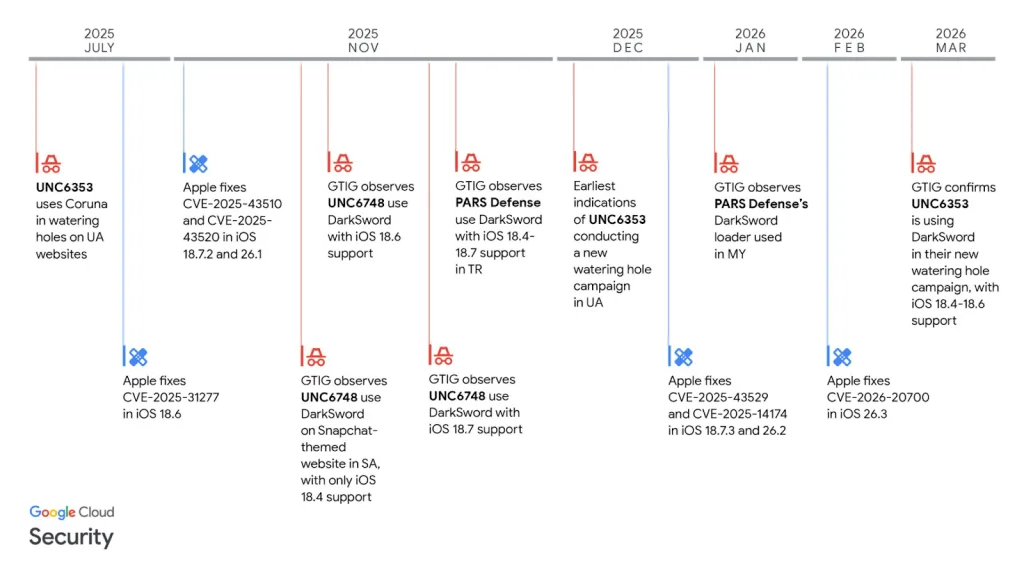
Google Threat Intelligence Group recently announced a new full-chain iOS exploit, DarkSword, that compromised iPhones by exploiting six zero-day flaws. The group said attackers have used it since at least November 2025. Google linked the activity to commercial surveillance vendors and suspected state-backed operators. The campaigns targeted users in Saudi Arabia, Turkey, Malaysia, and Ukraine.
According to Google, DarkSword works on iOS 18.4 through 18.7. It uses six vulnerabilities to gain remote code execution and install final-stage payloads. Researchers identified three malware families tied to successful compromises: GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. Google said the spread of one exploit chain across separate actors mirrors the earlier Coruna iOS exploit kit.
DarkSword Exploit Chain and Capabilities
Google said DarkSword chains six vulnerabilities to break into vulnerable iPhones. Three flaws affect WebKit, which powers Safari and all browsers on iOS and iPadOS. Two flaws sit in the iOS and macOS kernel. One targets Apple’s Dynamic Link Editor.
Lookout researchers described DarkSword as “a complete exploit chain and infostealer written in JavaScript.” They said the attack starts when Safari loads a malicious iframe hidden inside a webpage. From there, the chain escapes the WebContent sandbox and uses WebGPU to inject into mediaplaybackd.
The exploit then creates kernel read and write access. That access lets attackers reach privileged processes and loosen sandbox restrictions. As a result, the malware can reach protected parts of the filesystem. Thereafter, a main script runs several smaller components that gather passwords, encryption keys, and files before sending them to attacker-controlled servers.
Campaigns Spread Across Regions
Google researchers said UNC6748 used DarkSword in November 2025 against Saudi Arabian users through a Snapchat-themed website. In separate operations during November 2025 and January 2026, two campaigns linked to different PARS Defense customers targeted users in Turkey and Malaysia.
Google also tied DarkSword to UNC6353, a suspected Russian espionage group. The group had already used Coruna in an earlier activity. This time, it targeted Ukrainian users with DarkSword and a backdoor called GHOSTBLADE.
Researchers said GHOSTBLADE collected wide-ranging data from infected devices. The list included device details, installed apps, accounts, location history, photos, calendar entries, notes, cryptocurrency wallet data, account data, and Safari history. iVerify also analyzed that Ukrainian campaign.
Related: Google Warns of AI-Driven Malware Linked to North Korea Crypto Theft
Coruna Links and Suspicious Infrastructure
Two weeks earlier, Google Threat Intelligence Group and iVerify had disclosed Coruna, a spy-grade iOS exploit kit used in commercial surveillance operations, cyber espionage, and cybercrime. Google said Coruna contains five full iOS exploit chains and 23 exploits, including flaws with and without CVE identifiers. By comparison, DarkSword uses six vulnerabilities but reaches similar outcomes.
After the Coruna disclosure, Lookout researchers found another suspicious domain, cdncounter[.]net, linked to infrastructure previously associated with UNC6748. They said the domain shared technical traits with earlier malicious infrastructure and was connected to compromised Ukrainian websites carrying hidden iframes.
Further analysis showed the activity did not use Coruna. Instead, the injected code fingerprinted visiting devices and targeted select iOS versions with a different chain: DarkSword. What does it mean when the same exploit family can support both espionage and crypto theft?
Lookout said both Coruna and DarkSword can steal cryptocurrency as well as sensitive personal data. Researchers said that overlap leaves open two possibilities: financial motives, espionage goals, or a mix of both.




